How to install wordpress
Requirement: In order to install the wordpress use must have the following
requirement.
1. Wordpress setup.
2. Xamp server/wamp server.
Note: In order to install the
wordpress and Xamp setup downloard the setup from the given links below: http://www.wordpress.org , https://www.apachefriends.org/download.html
After the installation of the follow the followiunging
steps
1.
Downloard the setup of
wordpress from the above site show as
below and extract the file.
2.
Downloard the XAMPP server.
3.
Now place the wordpress file
in XAMP/htdocs
4.
Now run the XAMP by typing
localhost/wordpress on browser and click on create configuration file.
5.
After clicking the following
window appear click on lets go.
6.
After that enter the
information required as below.
8.
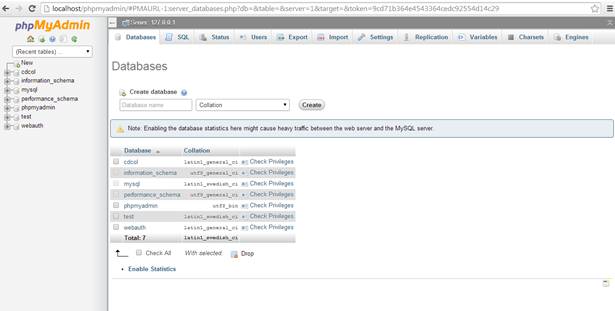
After clicking it will take
you to the php myadmin. Enter the database name.
9.
Now fill the following
information and click submit.
11. After running enter the
information and click on install wordpress.
12. After that it will take you
to the login page which as given
below.
This
is how the wordpress is being installed.














.png)
.png)

.png)

.png)
.png)
.png)
.png)
.png)
.png)













.png)